Hacker says he'll livestream deletion of Zuckerberg's Facebook page this sunday being the 30th day of September 2018 and he said we can login to our facebook page to...
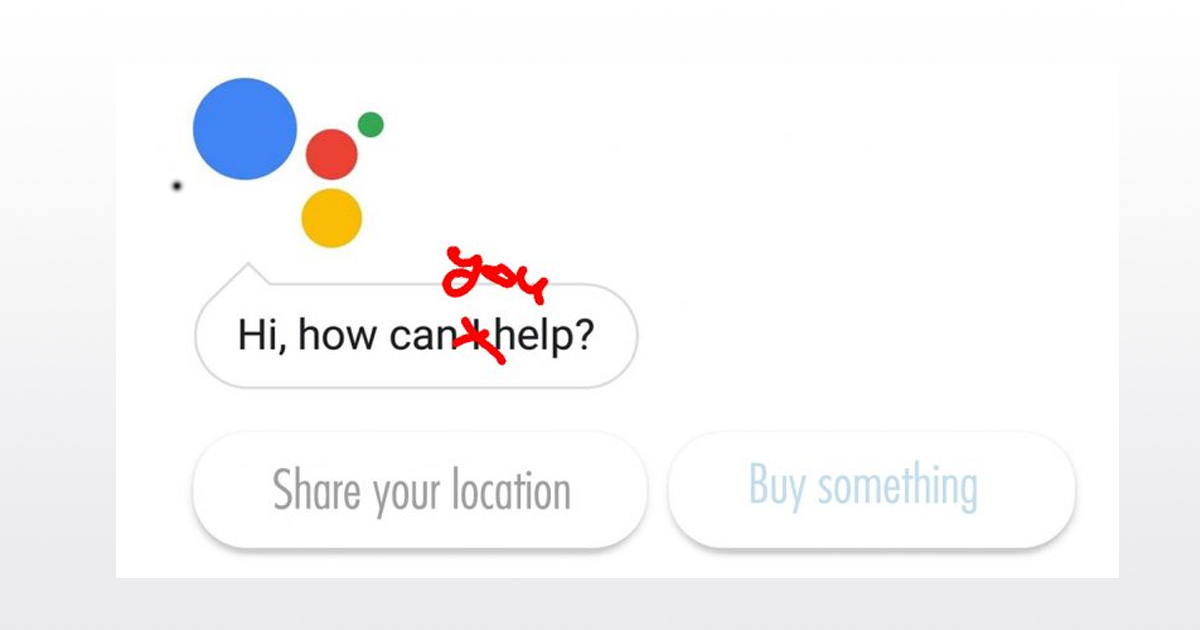
Without invading our privacy, does Google even have a business? Google is on a seemingly-ceaseless crusade to turn every one of its
Trump launches new national cyber strategy that aims to guide how the administration handles offensive and defensive cybersecurity and cyberthreats, Trump’s National Security adviser, John Bolton, told reporters in a...
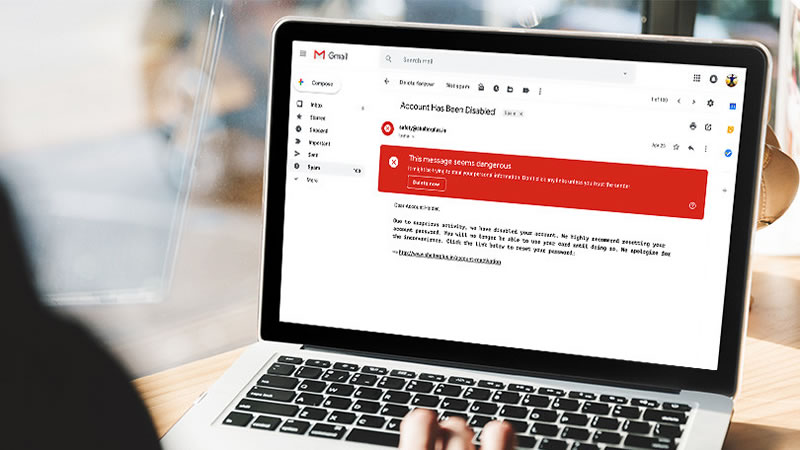
How to protect yourself from a data breach and here are the best ways to protect yourself and your information from identity theft and fraud.
Google said Apps Can Scan And Share Your Gmail Data With Consent. A year ago, Google ended its controversial email scanning practice.
Seven things small businesses must do to prevent cyber-attacks that we feel should be taken seriously as there has being series of cyber-attacks recently around the world and is...
If You Use Photoshop, Hackers Can Get Into Your Computer Right Now and this has being discovered by a security expert Kushal Arvind Shah of Fortinet's FortiGuard Labs cybersecurity and adobe...
How to Protect Your Personal Brand's Website From a Cyber is an important issue to look into as it has become a world problem.
Microsoft's New Monthly Charge for Windows 10 has been reviewed but we feel is going to be targeted to business rather than everyone.
The risks associated with global Internationalized Domain Names The risks associated with global internationalized domain names is posing some security challenges as many feels it has a dark side...